AspenTech V15: Powering the Future of Industrial Performance
Aspen Technology is pleased to announce the release of AspenTech V15—a transformative update designed to help organizations harness the full power of industrial AI, sustainability-driven innovation, and enhanced user experiences—all geared to helping customers improve operational performance.




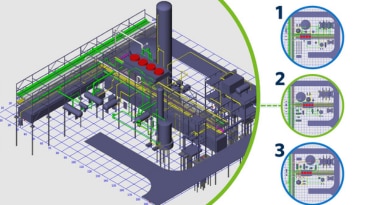







.png?la=en&h=415&w=675&hash=963166393FDED086664E34BCCD020E8B)

